Managing security in any institution is complex, and not just centered around technologies and individual products. When putting together a Security Operation Centre, SOC, you need to have all aspects covered. First, there’s the insight and requirements stipulated in the business plan. Also, keep in mind the security team’s skillset, abilities, responsibilities, and budget.
While we all want to feel secure, you will never be 100% protected from cyber threats and hacks. Even the most trusted security systems experience a breach. In such cases, the only thing that matters is the extent of the attack and the organization’s ability to secure its remaining data.
This means that the threat should only last for the shortest time possible. The only way to ensure this is having a system that is being continuously monitored. Also, having high levels of awareness of specific parameters is essential.
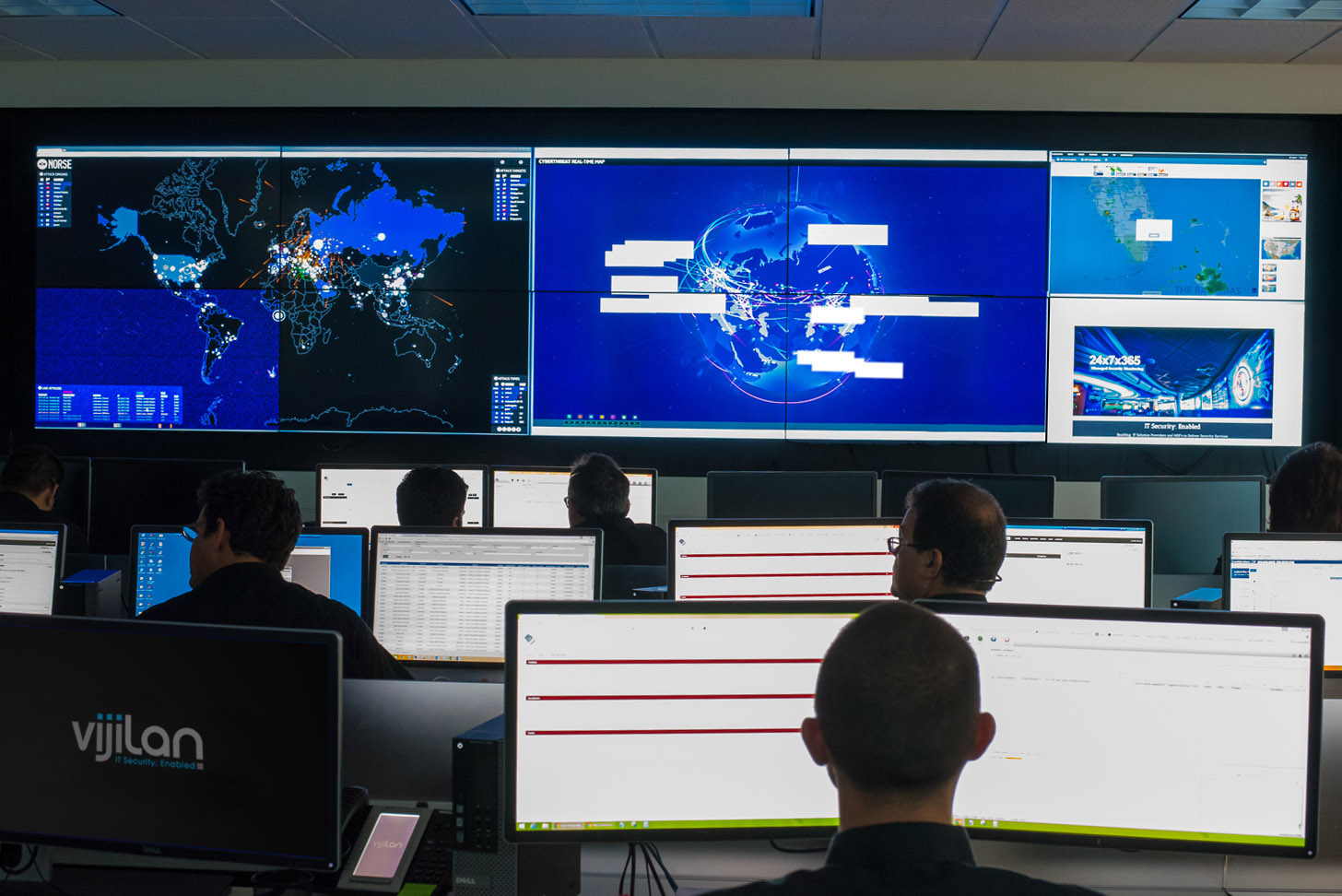
Therefore, a SOC is mandatory to help when facing cyber threats and keep companies on their toes in the worst-case scenario. The Security Operation Center is vital in cyber-security, which allows the security team to build setups, control security management measures, and assessments in line with your association. It will trigger an alarm in the event of a threat or a breach.
While setting up a security operation system can be troublesome and, to some levels intimidating, here are steps that will make the process easier to handle.
How to Work a Security Operation Center
First, note that your SOC will monitor your entire enterprise and evaluate all potential problems and likelihood of occurrence. It then successfully communicated these results to keep you in the know. The SOC is not the help desk. While the help desk looks into matters that affect an employee, the SOC runs through issues that affect the entire organization.
1. Get the right infrastructure
SOC is only as good as the tools utilized, therefore, you should make sure that you use the right devices to correct a data breach when it takes place. Some of the essential products include:
– SIEM tools
– Firewalls
– Data monitoring tools
– Asset discovery tools
– Automated application security
– Endpoint protection etc.
2. Build the right team
Your gadgets could be practical, but if the group using them is not effective then you are doing a zero job. It would be best if you have individuals who are good at:
- Tracking risks when looking for potential threats
- Carrying out framework monitors and overseeing alerts
- Examining an occurrence, managing an incident and proposing a solution
All of these require that the team stay prepared, thus being able to identify and interrupt a malware attack. A comprehensive budget to employ and keep such a team is crucial.
3. Host an Incident Response System
An IRS is critical for SOC since it will set the workflow depending on how incidents are detected.
4. Keep your premises protected
After all is said and done, you need to secure your business’s premises by collecting as much information as required.
At Vijilian labs, we can help you with the security operations you need. Speak to us for assistance today.